“We can’t add a virus scanner to our device or we’ll have to get re-certified by the FDA.” If you have any time in the trenches as a healthcare project manager, you have heard those words spoken by a medical device rep. Famous for falling back on the “FDA re-certification” argument, these words have clipped the wings of many a project security and usability requirement. Since many of these devices are sold by a few key players (Phillips, GE) healthcare providers had little choice but to grit their teeth and allow insecure hardware and software to be attached to their network. Then the real challenge begins as the quirky device(s) begins to show unexpected behaviors and generally fails to play well with standardized enterprise systems. If the healthcare organization deploys an operating system patch or places their standard endpoint protection on the device, they run the risk of the vendor halting support during a device issue until the offending patch or software is removed. This can quickly escalate into a patient safety issue, so many times organizations accept the risk and keep their medical devices unpatched and under-protected.
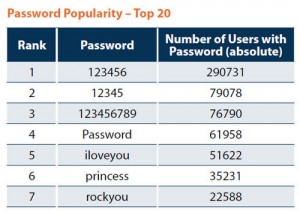
For years medical providers have petitioned the FDA to clarify the rules around cybersecurity and medical devices. Do device manufacturers have to re-certify every time they apply an operating system patch or install endpoint protection? The issue gained more urgency as HIPAA penalties for patient data breaches became more common. Organizations rightly questioned the re-certification argument from vendors since some of the most sensitive protected health information (PHI) is passed through or collected by these devices. How can organization’s effectively manage their security risks and protect against breaches if their key devices remain vulnerable to the most common security issues; outdated patches and endpoint protection? So healthcare IT had to get creative about protecting these devices. Separate medical VLANs, additional physical security, hamstrung endpoint protection and a lot of reluctant risk acceptance. While these steps help mitigate the risk of a breach, organizations still have to contend with similar issues that led to the recent Target credit card breach; default admin passwords, patching issues and third party system access.
Clarity on these concerns may finally be on the horizon. While not a strongly worded as some healthcare security and IT practitioners would like, the FDA has recently released (June 2013) a Safety Communication on the topic of medical devices and cybersecurity. It is the first series of memos and articles that point toward the FDA beginning to crack down on the issues of medical device security.
In my next post I will summarize the FDA Medical Device Safety memo as well as provide some additional thoughts on how to address this thorny problem. As always please feel free to leave comments below!